What Secure Productivity Really Means for IT Planning in 2026
Digital work in the Philippines has reached a scale where productivity is no longer confined to office hours, locations, or single systems. Cloud collaboration, hybrid access, and always-on communication now underpin day-to-day operations across enterprises, shared services centers, and BPO environments. For most organizations, this is no longer transformation. It is simply how work gets done.
What has changed is the risk environment surrounding that productivity.
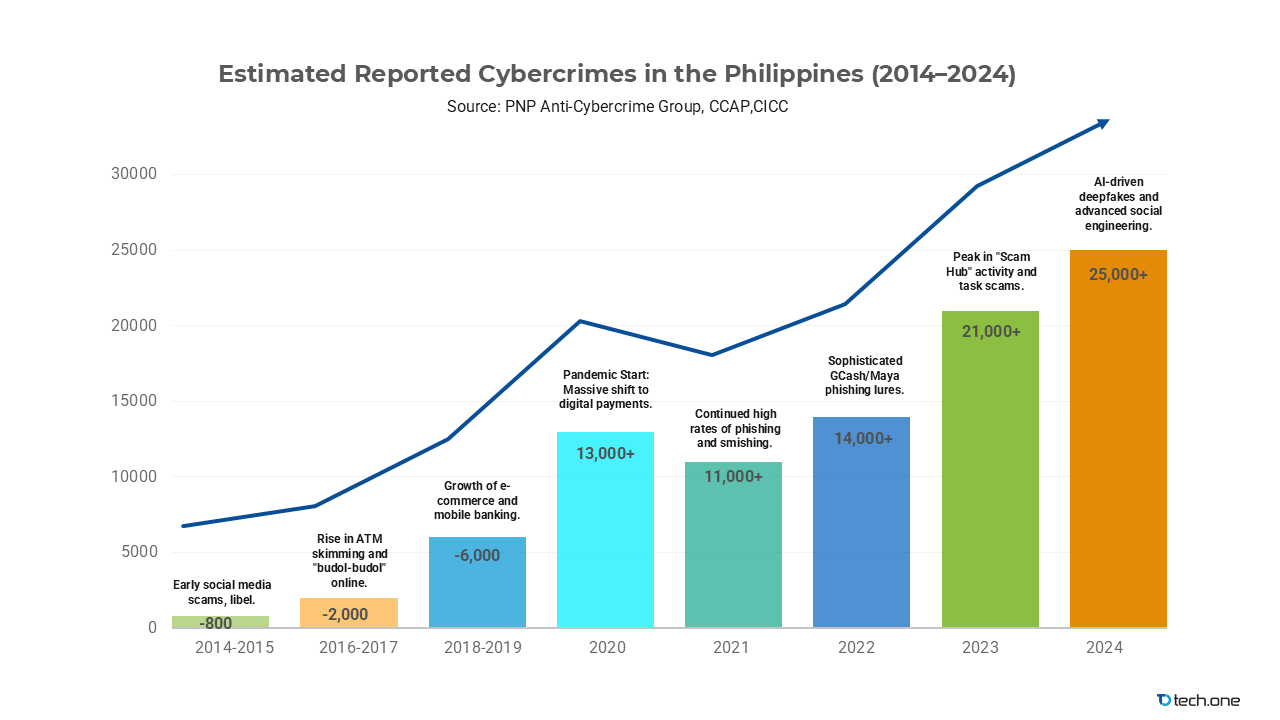
Recent cybersecurity reporting shows that the Philippines was among the top 20 most targeted countries for cyberattacks in 2025, with identity compromise, phishing, and business email compromise ranking among the most common attack methods. Industry studies also indicate that a large majority of Philippine organizations experienced multiple security incidents over the past year, many linked to third-party access, credential theft, or misuse of legitimate accounts.
What matters is not just the volume of attacks, but where they occur.
Work identities are now the primary entry point
Collaboration platforms and email are common attack paths
Incidents surface during normal business activity, not technical outages
The implication is structural. Productivity environments have become part of the threat surface. When access, sharing, and automation scale faster than governance and enforcement, risk accumulates quietly. It later manifests as operational disruption, regulatory escalation, and unplanned remediation cost.
This tension is already visible across common operating models. Shared services and BPO teams collaborate across time zones and external partners. Financial institutions expand digital services while navigating stricter data protection expectations. Enterprises rely on hybrid access where identity, device posture, and location change constantly.
In this context, productivity and security can no longer be treated as separate objectives. For 2026 planning cycles, secure productivity is not a configuration task or a user behavior problem. It is a planning condition that influences platform decisions, governance design, risk appetite, and budget prioritization.
This shift sits within a broader set of decisions facing IT leaders, explored in more detail in the 2026 IT Planning Guide for Philippine Organizations: Aligning Migration, Modern Work, AI, and Security where migration, Modern Work, AI, and security are examined as a single, interconnected strategy.
What “Secure Productivity” Actually Means
Secure productivity means an organization can move fast, collaborate freely, and adopt new capabilities without increasing risk, because identity, devices, data, and security controls are designed to work together as a single system.
In practical terms, secure productivity exists when:
- Employees can access what they need without relying on workarounds or informal exceptions
- Sensitive data remains protected even as it is shared, reused, and accessed remotely
- Security incidents are contained quickly without shutting down everyday operations
- New initiatives such as AI, automation, and partner collaboration can be introduced without re-engineering controls each time
Secure productivity is not about adding more tools, tightening policies indiscriminately, or expecting perfect user behavior. It is about structural alignment, so productivity gains do not quietly introduce operational, regulatory, or reputational risk.
For IT leaders planning toward 2026, this distinction matters. Productivity that depends on manual oversight or post-incident correction is fragile. Security that slows work or forces teams to bypass controls will not scale. Secure productivity exists only when speed and control are designed together, not traded off after the fact.
Why and When Secure Productivity Becomes a Planning Issue
Most IT leaders already have the core components of secure productivity in place. Identity platforms are deployed. Collaboration tools are embedded in daily work. Endpoint controls and security policies exist across the environment. The challenge in 2026 is no longer access to capability. It is whether those capabilities still operate coherently under current working conditions.
Over the past few years, productivity environments have evolved faster than the structures governing them. Hybrid work blurred internal and external boundaries. Collaboration shifted from centralized repositories to persistent chat, shared workspaces, and external guests. Automation and AI accelerated how information is accessed, reused, and acted upon. These changes created tighter dependencies between identity, data, devices, and security, dependencies that were never designed as a single system.
Most organizations adapted incrementally. Collaboration was enabled to maintain continuity. Access expanded as users, partners, and contractors increased. Security tools were added in response to incidents. Governance existed, but enforcement varied by platform, team, or use case.
Each decision made sense at the time. Together, they produced environments that function well until pressure is applied.
That pressure is now routine.
Secure productivity becomes a planning issue when productivity scale, security risk, and operational expectations intersect. This typically happens when organizations reach one or more of the following points:
- Productivity platforms become mission-critical to revenue, payroll, customer operations, or regulated processes
- Identity and collaboration incidents begin to trigger legal, regulatory, or executive escalation
- AI, automation, or expanded partner access is planned, but access and data trust are uncertain
- Security decisions start to affect budgets, licensing, and business timelines rather than configurations
At this stage, configuration changes alone are no longer sufficient. Questions emerge that cannot be solved inside a single platform or team:
- How much friction is acceptable in daily work, and where
- Which access paths are non-negotiable, and which can be adaptive
- Who owns risk decisions when productivity and security conflict
- How investments should be sequenced to reduce exposure without stalling the business
These are planning questions. They require prioritization, trade-off decisions, and budget alignment. Treating secure productivity as a configuration exercise at this point leads to reactive controls, user workarounds, and delayed initiatives.
Treating it as a planning condition allows organizations to scale work, adopt AI, and meet regulatory expectations without re-negotiating security after every change.
What Changed Heading Into 2026: Three Forces IT Leaders Can’t Ignore
The challenge itself is not new. What makes 2026 different is the convergence of scale, speed, and exposure inside everyday work environments.
1. Always-On Work Has Become the Default
Work now unfolds across chat threads, shared documents, mobile approvals, and ad hoc meetings that cut across teams and time zones. Context switching is constant. Decisions are made under time pressure, often outside formal workflows.
Controls designed for structured, linear work struggle in this environment. They assumed predictable access patterns and deliberate requests. That assumption no longer holds.
Planning implication: Controls must work when people are rushing and multitasking. If productivity depends on perfect user behavior, it will fail. Governance must be embedded into workflows rather than layered on top.
2. Identity Is the Control Plane
Attackers increasingly bypass infrastructure and target identities directly. Compromised credentials provide immediate access to email, files, collaboration platforms, and business applications.
When identity becomes the control plane, every productivity decision becomes an access decision. Who can approve, share, automate, or interact with AI tools is inseparable from risk management.
Planning implication: Identity strategy cannot stop at sign-in success. Conditional access, session risk, and privilege boundaries must be considered before scaling automation and AI-enabled workflows.
3. Digital Expansion Is Outpacing Governance Models
Organizations continue to expand digital channels, partner ecosystems, and outsourced operations. Each expansion increases productivity reach, but also multiplies access paths and accountability gaps.
Traditional governance models struggle to keep pace because they were designed for smaller, more centralized environments.
Planning implication: Productivity and governance must scale together. Without intentional design, growth introduces exposure that surfaces later as audit findings, incident response disruption, or forced restrictions that slow the business.
The Five Pillars of Secure Productivity
Productivity environments rarely fail because tools are missing. They fail because foundational elements were never designed to operate together at scale.
In most organizations, identity, endpoints, collaboration, data protection, and threat response evolved independently. Each domain may be adequate on its own. The breakdown occurs when work accelerates and those domains are forced to function as a single system.
The pillars below represent structural requirements for productivity that remains usable, defensible, and resilient under real operating pressure.
Pillar 1: Identity That Holds Up Under Pressure
Identity now governs access to productivity, data, and automation. In local enterprises, complexity is amplified by shared service models, frequent contractor turnover, and executives approving actions from mobile devices.
Resilient environments focus less on stronger credentials and more on confidence in access decisions.
By 2026, identity operates dynamically:
- Access adapts based on risk, not just role
- Privileged rights are time-bound
- High-risk actions are protected without disrupting routine work
This requires evaluating identity controls alongside productivity workflows, not after incidents. Platforms such as Microsoft Entra ID support this approach when used to enforce risk-based access and just-in-time privilege elevation.
Signals to watch
- Time to detect and disable compromised accounts
- Coverage of strong authentication for privileged roles
- Reduction in standing administrative access
Pillar 2: Endpoints That Don’t Undermine Productivity
Productivity happens on endpoints, not in policy documents. In Philippine organizations, corporate laptops, personal devices, shared machines, and mobile phones coexist by necessity.
When endpoint posture is inconsistent, productivity environments inherit that risk.
Secure productivity requires endpoints that:
- Meet minimum compliance standards before accessing sensitive workloads
- Protect work data even on mobile or shared devices
- Remain visible without constant user intervention
Endpoint management approaches, such as those enabled through Microsoft Intune, provide consistency without enforcing a single-device model.
Signals to watch
- Percentage of users on compliant devices
- Patch and update latency
- Incidents linked to unmanaged endpoints
Pillar 3: Collaboration That Moves Fast Without Losing Control
Collaboration is where secure productivity most often breaks down. In high-velocity environments, controls that slow people down are bypassed.
Secure productivity designs guardrails that work at speed:
- Internal sharing by default, controlled external access
- Clear data handling expectations within workflows
- Visibility into where sensitive content is shared
Rather than relying on cleanup after incidents, collaboration platforms such as Microsoft Teams and SharePoint are governed through consistent lifecycle and sharing policies, supported by targeted data classification.
Pillar 4: Data Protection That Aligns with Regulatory Reality
In the Philippines, data protection expectations are no longer theoretical. Regulatory scrutiny from bodies such as the National Privacy Commission and sector-specific regulators continues to increase. At the same time, data now lives primarily inside collaboration platforms rather than centralized repositories.
This creates a gap between policy intent and operational enforcement.
Secure productivity environments address this by making data protection usable and observable:
- Classification schemes are simple enough to apply consistently
- Retention rules align with both operational needs and regulatory timelines
- Investigation and discovery processes are prepared before incidents occur
Tools such as Microsoft Purview support these outcomes, but the differentiator is planning discipline. Data governance is designed to support productivity, not interrupt it during audits or investigations.
Signals to watch
- Percentage of data covered by retention and classification policies
- Time required to respond to audit or investigation requests
- Frequency of manual exceptions
Pillar 5: Threat Protection That Preserves Business Continuity
The final pillar determines whether productivity survives contact with reality.
Most successful attacks today do not rely on advanced exploits. They exploit legitimate access paths, phishing users into approving actions or reusing credentials. When detection and response are fragmented, productivity grinds to a halt during investigations.
Secure productivity requires threat protection that is integrated into how work actually happens.
By 2026, resilient environments demonstrate:
- Correlated visibility across identity, email, endpoints, and cloud activity
- Standardized response playbooks for account compromise and phishing incidents
- Faster containment that limits disruption to users and business operations
Extended detection and response capabilities, such as those provided through Microsoft Defender and centralized security platforms, support this integration when aligned with clear operational processes.
Signals to watch
- Mean time to detect and respond
- Number of incidents contained without business disruption
- Reduction in repeat phishing or account takeover events
Why These Pillars Matter Together
Each pillar addresses a different dimension of productivity risk. None of them work in isolation.
Weak identity controls undermine collaboration security. Inconsistent endpoints weaken access decisions. Poor data governance amplifies incident impact. Fragmented threat response disrupts operations even when controls exist.
Together, these pillars provide a way to assess whether productivity gains are structurally sound or dependent on fragile workarounds.
What to Prioritize First: A Practical 30-60-90 View
One of the reasons secure productivity initiatives stalls is that they are framed as long-term transformations. For most IT leaders, the challenge is not knowing what “good” looks like. It is deciding where to start without disrupting the business.
A 90-day planning horizon creates focus. It forces trade-offs, limits scope and makes progress measurable. More importantly, it allows leaders to reduce risk quickly while setting conditions for broader 2026 initiatives such as AI adoption, platform consolidation, or regulatory readiness.
The objective of the first 90 days is not perfection. It is to establish minimum viable secure productivity, where the most common failure points are addressed and governance begins to operate predictably.
Days 0–30: Establish Non-Negotiable Baselines
The first phase focuses on controls that prevent disproportionate damage when something goes wrong. These are foundational and should not depend on user behavior or manual oversight.
Priority actions in this window typically include:
- Enforcing strong authentication for privileged and high-impact roles, including executives and administrators
- Reviewing and tightening privileged access so rights are time-bound rather than permanent
- Defining default collaboration and external sharing behaviors that reflect current risk appetite
- Establishing a minimum device compliance baseline for access to core productivity workloads
This phase often surfaces uncomfortable truths about access sprawl and legacy exceptions. Addressing them early prevents larger disruptions later.
Days 31–60: Reduce Friction Without Increasing Risk
Once baselines are in place, attention can shift to usability. Secure productivity fails when controls are correct but inconvenient.
In this phase, organizations focus on making secure behavior the easiest path:
- Simplifying access requests and approvals through identity workflows
- Standardizing how collaboration spaces are created, named, and retired
- Applying a small number of meaningful data classifications to high-risk content types
- Reducing reliance on ad hoc workarounds that bypass controls
This is where productivity visibly improves. Teams spend less time navigating exceptions, and IT spends less time responding to avoidable access and sharing issues.
Days 61–90: Operationalize and Make It Stick
Controls that are not operationalized degrade quickly. The final phase ensures secure productivity survives real incidents and daily pressure.
Key focus areas include:
- Defining and rehearsing incident response playbooks for common scenarios such as account compromise or phishing
- Establishing reporting that ties productivity signals to risk indicators, not just activity metrics
- Aligning IT, security, and business stakeholders on escalation paths and decision ownership
By the end of this phase, secure productivity should no longer depend on individual heroics. It becomes part of how the organization operates.
- Productivity improvements require exceptions, manual approvals, or parallel tools
- Incidents disrupt operations because response depends on human coordination rather than built-in controls
These constraints force reactive trade-offs. Leaders are asked to choose between speed and control, innovation and compliance, productivity and resilience.
When secure productivity is established, the planning conversation changes:
- AI readiness becomes a question of prioritization, not feasibility
- Platform and licensing decisions can be simplified instead of expanded
- Security investments shift from coverage to effectiveness
- Incidents are absorbed with less disruption to day-to-day work
In practical terms, secure productivity does not eliminate risk. It reduces the cost of change. It allows organizations to introduce new capabilities, partners, and automation without re-negotiating controls each time.
For 2026, that flexibility is often the difference between plans that are technically sound and plans that are actually executable.
Why This Matters for 2026 Planning
When secure productivity is weak, planning conversations stall. AI initiatives remain limited. Security spend grows without proportional outcomes. Incidents disrupt operations.
When secure productivity is established, planning changes. AI readiness becomes feasible. Platform decisions simplify. Security investment shifts from coverage to effectiveness. Change becomes less costly.
Secure productivity does not eliminate risk. It reduces the cost of change. That flexibility often determines whether 2026 plans are executable.
Strengthening Secure Productivity Before Gaps Define Outcomes
Gaps in Modern Work environments rarely fail loudly. They accumulate quietly across identity, access, collaboration, and data sharing until productivity itself becomes the risk surface. When incidents occur, the root cause is rarely missing tools—it is controls that were never fully aligned with how work actually operates.
For organizations planning through 2026, closing these gaps early is one of the most effective ways to reduce breach likelihood, limit business disruption, and demonstrate defensible governance as digital work scales. It is also a clear indicator of whether current Modern Work foundations can support AI, automation, and external collaboration without increasing exposure.
Reaching this level of readiness requires more than feature enablement. It demands consistent enforcement, integrated visibility, and controls proven to work under real operating conditions.
Tech One Global Philippines works alongside organizations as a long-term Modern Work and security partner. As 4-time Microsoft Partner of the Year with Microsoft Solutions Partner Designation in Modern Work with Advanced Specializations in Adoption and Change Management, Teamwork Deployment, Meetings and Meeting Rooms for Microsoft Teams, and Calling for Microsoft Teams Modernize Endpoints and Security with Advanced Specializations in Cloud Security, Identity and Access Management, Information Protection and Governance, Threat Protection, and Copilot,, we help leadership teams translate Microsoft capabilities into enforceable, auditable controls that support secure productivity at scale.
Organizations best positioned for 2026 will not be those that react fastest to incidents—but those that strengthen secure productivity foundations early, with controls that are consistent, integrated, and operationally proven.
Prepare for 2026 with security foundations designed for Philippine operating realities, implemented by experts who understand local risk, compliance expectations, and enterprise constraints.