2026 IT Planning Guide for Philippine Organizations: Aligning Migration, Modern Work, AI, and Security
2026 will not be defined by whether organizations adopt cloud, AI, or modern work technologies, but by whether these capabilities can be operated securely, efficiently, and at scale.
Over the past few years, many organizations in the Philippines have made meaningful progress in digital transformation. Core workloads have moved to the cloud, and executive discussions increasingly include analytics and AI. In practice, however, IT leaders are encountering a growing gap between technology adoption and operational readiness.
In fact, in the Philippines, there is a growing trend of companies rushing to adopt AI without the necessary skills, creating a significant ‘readiness gap’ where 80% of organizations feel intense pressure to integrate AI, yet only 12% are actually equipped with the strategy and infrastructure to deliver measurable value.
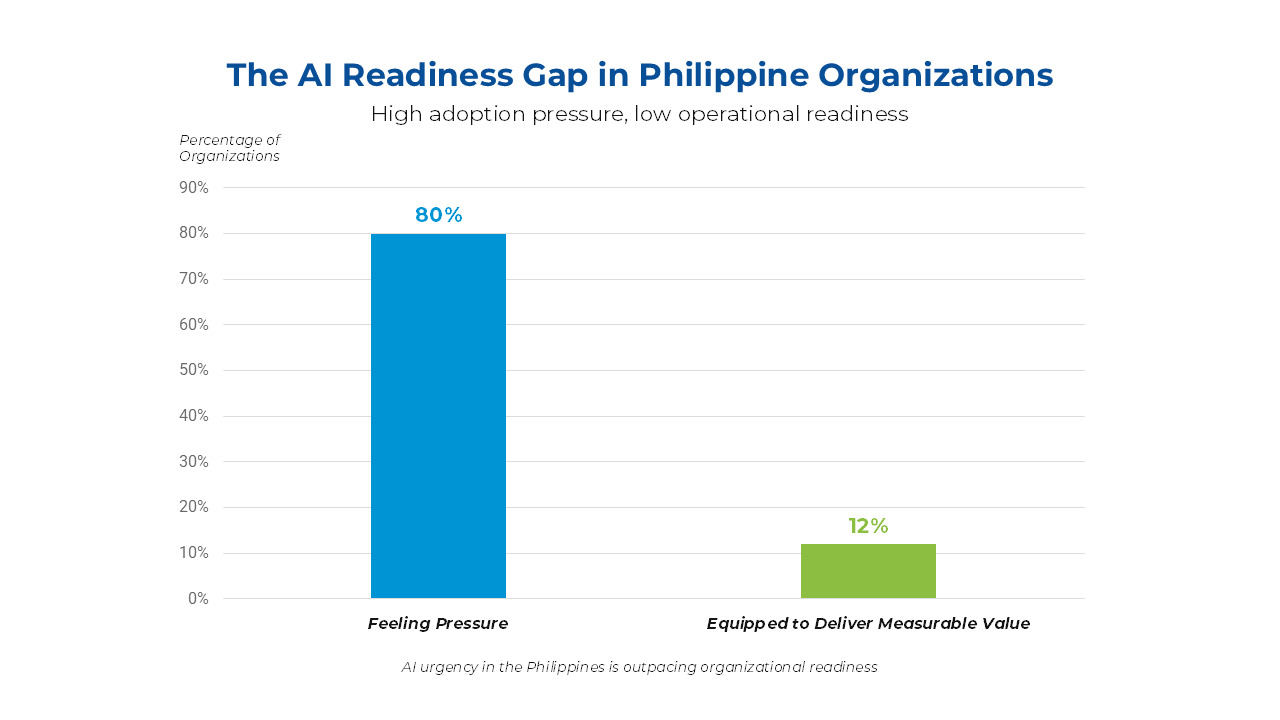
This shows us that the challenge is no longer technology availability, but planning, integration, and operational discipline.
In our work with organizations across the Philippines, Tech One consistently observes the same pattern. Migration, productivity, AI, and security are planned as separate initiatives, often owned by different teams, funded in different cycles, and measured against different success criteria. The result is higher cost, slower execution, and unnecessary risk. More importantly, this fragmentation prevents organizations from realizing the full value of Microsoft’s ecosystem, where each layer is designed to reinforce the others when implemented with intent.
IT leaders face a narrow but important window to reset this approach, particularly in Q1. Decisions related to migration priorities, licensing strategy, Modern Work optimization, AI readiness, and security posture will shape not only budgets, but also the organization’s ability to innovate without increasing exposure.
This guide is designed for CIOs, CISOs, IT Directors, and business leaders in the Philippines who are navigating these decisions. It provides a decision-oriented perspective to assess current readiness, identify what needs to be addressed first, and align migration, Modern Work, AI, and security into a single, coherent 2026 IT strategy grounded in Microsoft best practices and informed by regional realities.
I. Cloud Migration: Establishing a Stable Foundation for 2026
Cloud migration is now an operational baseline for most large organizations in the Philippines. Core workloads already run across hybrid and cloud environments. The question facing IT leaders is no longer whether migration has occurred, but whether the current state of migration can support what the business now expects from IT.
Existing migration outcomes are being tested against new demands. These include secure hybrid work, real-time analytics, AI-enabled productivity, and resilience against increasingly sophisticated cyber threats. Many environments were not designed with these outcomes as primary objectives, creating cost, security, and scalability constraints that now require reassessment.
What to Reassess Based on Your Current Cloud Operating Model
Before deciding whether a change in cloud platform or architecture is necessary, IT leaders need to check if their current setup is enabling them to scale or stalling their growth.
If You Are Operating Primarily On-Premise
Some organizations remain on-prem by design due to regulatory, latency, or operational constraints. Others remain there because modernization has stalled.
When modernization stalls, the environment often becomes stable but inflexible. Systems continue running, but adapting to new security models, workforce tools, or resilience requirements becomes increasingly difficult.
Time to reassess your platform if:
- Core applications are tightly coupled to legacy infrastructure with limited vendor support
- Security controls rely heavily on network perimeter rather than identity and access
- Scaling capacity or enabling resilience requires manual provisioning and long lead times
- Modern analytics, collaboration security, or AI initiatives require complex workarounds
What this signals: On-prem environments that were sufficient for stability often struggle to support modern tools, new security models, and upgraded workforce platforms. Over time, this increases operational risk, slows recovery during incidents or natural disruptions, and raises long-term cost despite appearing “under control” day-to-day.
If You Are Operating in a Hybrid Cloud Model
Hybrid cloud is the most common reality for Philippine organizations. It can offer flexibility, regulatory alignment, and phased modernization when managed deliberately.
It becomes difficult to sustain when growth outpaces architectural alignment and identity governance.
Time to reassess your platform if:
- Identity and access controls differ between on-prem and cloud environments
- Security baselines are inconsistent or manually enforced across platforms
- Application dependencies limit workload mobility or modernization
- Cloud costs increase without clear visibility into business value or risk exposure
- Teams operate separate tools and processes across environments
What this signals: Hybrid itself is not the problem. Uncoordinated hybrid growth is. Over time, fragmented platforms can limit security consistency and slow future initiatives. When hybrid environments are simplified, standardized, and identity-driven, they can remain an effective transitional or long-term model.
If You Are Operating Fully in the Cloud
A well-designed full cloud model offers the greatest potential for scalability, built-in resilience, and consistently enforced security. However, being “fully cloud” does not automatically mean being optimized or future-ready.
Time to reassess your platform if:
- Early lift-and-shift architectures remain largely unchanged years later
- Identity, networking, and security designs still reflect on-prem assumptions
- Cost optimization requires constant manual intervention
- Platform choices limit adoption of advanced security, data governance, or AI capabilities
- Teams rely on compensating controls rather than native platform capabilities
What this signals: Full cloud environments deliver the strongest outcomes when architecture evolves alongside business and security requirements. When designed intentionally, they simplify identity governance, improve resilience and disaster recovery, and enable faster adoption of modern workforce and AI capabilities.
Across all operating models, the question is no longer whether systems are stable today, but whether the platform can support stronger security, predictable costs, and resilience as demands rise.
As complexity increases, environments that consolidate identity, security, and recovery under a unified cloud operating model tend to scale with fewer trade-offs. For many organizations planning toward 2026, cloud strategy is becoming less about location and more about choosing the operating model that removes constraints instead of adding them.
Why the Right Cloud Platform and Strategy Enable Operational Excellence and Business Continuity and Disaster Recovery (BCDR)
The right cloud platform and strategy matter because they define how well an organization can operate under pressure, recover from disruption, and adapt without accumulating hidden risk.
Operational excellence depends on consistency, visibility, and automation. When cloud platforms are selected or expanded without architectural intent, day-to-day operations become harder to manage over time.
A well-aligned cloud strategy enables operational excellence by:
- Reducing manual intervention
Integrated identity, security, and operations reduce reliance on ad hoc processes and exception handling.
- Improving visibility and control
Centralized monitoring and governance make it easier to understand performance, risk, and cost across environments.
- Supporting predictable scaling
Capacity, security, and access controls scale together instead of being retrofitted as demand increases.
When these elements are missing, IT teams spend more time keeping systems running and less time improving reliability or resilience.
Why Cloud Platform Choice Shapes BCDR Outcomes
Business Continuity and Disaster Recovery (BCDR) is not something added after migration. It is largely determined by the platform’s native ability to support resilience, recovery, and coordinated response.
The right cloud platform strengthens BCDR because it:
- Enables faster, more reliable recovery
Built-in redundancy, backup, and failover reduce dependency on manual recovery steps during incidents.
- Simplifies recovery planning
Consistent architectures make it easier to test, validate, and execute recovery scenarios. - Limits blast radius during disruptio
Identity-driven access and segmentation help contain incidents without shutting down entire environments. Organizations running on fragmented platforms often discover during an incident that recovery depends on people and workarounds, not systems.
Operational excellence and Business Continuity and Disaster Recovery (BCDR) are no longer separate objectives. Both depend on whether the cloud platform and architecture can absorb change, contain disruption, and recover without forcing the business to slow down.
Organizations that choose platforms designed for integrated identity, security, and resilience reduce operational friction and recover faster when incidents occur. Those that do not often compensate later with additional tools, manual processes, and higher risk exposure. The strategic advantage lies in selecting a cloud platform and operating model that support stable operations today and credible recovery when it matters most.
II. Modern Work: Preparing the Workforce for AI and Security Demands
Modern Work platforms are firmly embedded in daily operations across Philippine organizations. Collaboration, communication, and document management are no longer transformation initiatives. They are core business infrastructure.
However, widespread deployment has not always translated into measurable value. Many environments were implemented rapidly to support hybrid work, prioritizing continuity over optimization and governance. As expectations shift toward productivity, compliance, and risk management, the gap between deployment and maturity has become more apparent.
How Under-Optimized Modern Work Environments Typically Appear
Across organizations, several patterns indicate that Modern Work is not delivering its full potential:
- Employees rely on basic collaboration features, while document workflows and knowledge management remain inconsistent
- Security and compliance teams deploy additional tools because native capabilities are not fully enabled
- Limited visibility exists into how sensitive data is accessed, shared, and stored
- IT leaders struggle to connect Modern Work investment to measurable productivity or risk outcomes
In these conditions, Modern Work functions primarily as a communication layer rather than a governed digital workspace.
Why Choosing a License Becomes a Strategic Question
Licensing is often treated as a procurement decision. In practice, it is an architectural one. Many organizations continue operating on license plans selected during earlier adoption phases, when workforce needs and risk profiles were more limited.
License selection directly affects which security and compliance controls are available, how identity and data protection policies are enforced, and whether additional tools are required to address gaps.
When licensing is misaligned with current requirements, organizations either overspend on overlapping solutions or accept avoidable operational and security risks. This is why license reassessment often surfaces early in the year alongside budget planning and roadmap validation.
If Upgrades Are Not Immediate: How to Maximize Existing Plans
Not every organization is positioned to upgrade licenses immediately. In many cases, meaningful value can still be realized by optimizing existing plans.
Key focus areas include:
- Configuration and governance
Ensure collaboration tools follow consistent structures, retention policies, and access controls aligned with business and regulatory requirements.
- Security feature activation
Enable and correctly configure available controls related to identity, device access, and data protection to reduce reliance on external tools.
- Usage alignment
Guide teams toward intended workflows and reduce informal workarounds that introduce inefficiency and risk.
Why this matters: Underutilized features represent both wasted investment and unmanaged exposure. Optimization strengthens security posture and establishes a more stable platform for future capability expansion.
How Organizations Prepare the Workforce for AI and Security Demands
AI will only work if people are ready to use it securely. If daily work habits are misaligned, productivity gains quickly turn into risk.
1. Start With Role Clarity, Not Broad Enablement
AI amplifies whatever access and behaviors already exist. When roles and decision boundaries are unclear, AI accelerates confusion and exposure rather than value.
Effective organizations define:
- Which roles are authorized to use AI-assisted features and for what purposes
- Which data sources are in scope and which are excluded
- Where human review or approval remains required
This approach respects workforce expertise while avoiding blanket enablement that later requires restriction.
2. Standardize Ways of Working Before Scaling AI
AI exposes inconsistency. Teams that store content differently or rely on informal sharing struggle to benefit from AI without creating sprawl.
Preparation focuses on:
- Standard collaboration structures for teams and projects
- Clear ownership of content and workspaces
- Defined lifecycle rules for documents, chats, and shared spaces
These standards reduce friction for employees and ensure AI operates on governed, reliable information.
3. Embed Security Expectations Into Daily Workflows
Security readiness is achieved when secure behavior is the default, not an exception.
Organizations close gaps by:
- Making secure sharing the easiest option
- Embedding access and data protection controls directly into collaboration tools
- Ensuring identity and device checks align with how people actually work
When security fits the workflow, adoption improves and workarounds decline.
4. Treat Enablement as Continuous, Not Event-Based
One-time training does not prepare employees for evolving AI and security demands. Readiness improves when guidance is reinforced through real use cases.
Effective programs include:
- Short, role-specific guidance tied to actual workflows
- Clear escalation paths for uncertainty around data or AI outputs
- Regular review of usage patterns to adjust controls and guidance
The goal is confidence and consistency, not compliance theater.
5. Use Partners to Accelerate Maturity, Not Replace Ownership
Certified partners and training programs are most effective when they strengthen internal capability rather than substitute for it.
Organizations gain the most value when partners help:
- Translate platform capabilities into enforceable workflows
- Validate configurations against real operating scenarios
- Accelerate maturity in areas requiring specialized expertise
This allows internal teams to retain ownership while reducing trial-and-error.
Without deliberate workforce preparation, AI and Modern Work initiatives stall. With it, organizations gain confidence to scale productivity without increasing exposure.
Modern Work as an Indicator of Organizational Readiness
Modern Work platforms now sit at the center of daily operations. They shape how employees access information, share data, and execute business processes. As a result, the quality of Modern Work implementation has become a practical indicator of broader organizational readiness.
Where access controls, data governance, and identity policies are inconsistently applied, gaps surface quickly in daily operations. These gaps increase friction, complicate compliance, and limit the organization’s ability to introduce new capabilities without increasing risk. Environments with clear governance and enforced standards, by contrast, allow change to be introduced with greater predictability.
Modern Work is no longer a rollout milestone. It is an ongoing management responsibility that directly affects productivity, security, and readiness for what comes next
For many organizations, this shift introduces difficult trade-offs between productivity, security, and operational control. Understanding how these elements come together in practice is critical to planning Modern Work environments that support the business without increasing risk.
Now, the harder question is no longer how to enable productivity, but how to do so without increasing security exposure or operational complexity. This tension, and how it should shape 2026 planning decisions, is explored further in What Secure Productivity Really Means for IT Planning in 2026.
III. How Organizations Close the AI Readiness Gap
AI is no longer a future-state capability. It is already embedded into daily work through search, content drafting, data summarization, and decision support. Employees expect faster answers, less manual effort, and better access to institutional knowledge. Business leaders expect measurable productivity gains.
What many organizations are discovering is that AI adoption does not fail because of the tools themselves. It fails because everyday work environments were not designed to support AI safely at scale.
In practice, AI readiness has become a question of operational discipline, not innovation appetite.
Why AI Has Become a Workforce Reality, Not an Experiment
AI is now woven into how work happens. Documents are drafted collaboratively. Meetings generate transcripts and summaries. Employees ask questions about enterprise data instead of searching for file shares. These behaviors are already occurring, whether formally enabled or not.
The shift matters because AI amplifies whatever foundations already exist.
- If access controls are loose, AI accelerates oversharing.
- If data is poorly governed, AI increases exposure.
- If identity signals are weak, AI expands the blast radius of misuse.
This is why many early AI initiatives stall. Leaders recognize the potential but hesitate to scale because they cannot confidently answer basic questions about data access, accountability, and control.
How Leaders Know It’s Time to Address AI Readiness
For most organizations, the readiness gap becomes visible before AI is formally deployed.
Common signals include:
- AI pilots remain isolated to small teams because leadership is uncomfortable expanding access
- Security and compliance teams raise concerns about data leakage, but lack clear guardrails
- Business users experiment with AI features, while governance discussions lag behind
- IT struggles to explain which data AI can safely access and why
These are not failures. They are indicators that readiness work must come before expansion.
AI readiness is less about “turning AI on” and more about ensuring that existing productivity environments can support AI use without introducing uncontrolled risk.
The Real Readiness Question: Can the Environment Support AI Responsibly?
Before scaling AI, organizations must be able to answer three practical questions.
- Can AI access the right data, and only the right data?
This requires structured, discoverable information with clear classification and access boundaries.
- Can AI actions be traced and explained?
Identity, logging, and audit controls must support investigation, not just usage.
- Can misuse be detected and contained quickly?
Security controls must extend into collaboration and data access patterns, not sit outside them.
When these conditions are unclear, AI adoption tends to slow or proceed cautiously, often limited to non-critical use cases.
Where AI Introduces New Security Risk
AI does not introduce entirely new threat types. It magnifies existing ones.
The most common risk areas include:
- Data exposure at scale
AI can surface sensitive information faster than manual search, increasing the impact of misclassification or overly broad access.
- Privilege amplification
AI acting on behalf of a user inherits that user’s permissions. Weak identity controls become more dangerous, not less.
- Reduced visibility into misuse
Without clear auditing and investigation workflows, it becomes harder to distinguish legitimate AI use from inappropriate access.
These risks are not theoretical. They are extensions of identity, data, and collaboration issues that already exist in many environments.
How Organizations Actually Close the AI Readiness Gap
Organizations that scale AI successfully do not start with advanced use cases. They start by strengthening foundations that already support everyday work.
Effective readiness efforts focus on:
- Data discipline
Ensuring information is classified, discoverable, and protected in ways that reflect real business use.
- Identity confidence
Enforcing accurate access, minimizing standing privilege, and improving visibility into who can act on what data.
- Governance clarity
Defining acceptable use, ownership, and response processes before issues arise.
- Security integration
Treating AI as an extension of Modern Work, subject to the same containment and response expectations.
These steps rarely feel like “AI projects,” but they are what allow AI initiatives to move beyond pilots without stalling.
Why Readiness Comes Before Scale
Organizations that invest in readiness first see more predictable outcomes when AI is introduced more broadly.
They gain faster access to trusted knowledge without increasing data sprawl. They reduce manual effort across finance, HR, operations, and IT without introducing audit risk. They expand AI use cases with confidence rather than hesitation.
Most importantly, they avoid the cycle where AI ambition outpaces governance, forcing leaders to slow down just as value becomes visible.
Closing the AI readiness gap is not about delaying innovation. It is ensuring that when AI becomes part of everyday work, it strengthens productivity instead of quietly increasing exposure.
IV. Security: Determining Whether the Environment Can Withstand Real-World Attacks
As environments become more interconnected and access to information accelerates, security has become the control layer that governs everything else. Traditional perimeter-based models are no longer sufficient in hybrid and cloud-first organizations, where identity, collaboration, and data move continuously across platforms.
Security readiness in 2026 is defined less by how many tools are deployed and more by whether those tools operate as a single system. The critical question is not coverage, but whether the organization can detect, contain, and recover from an attack without significant business disruption.
Are You Prepared for an Actual Security Incident?
Many organizations still measure security maturity through compliance checklists or tool inventories. Real incidents expose a different reality.
Microsoft’s Digital Defense Report consistently shows that the majority of successful attacks rely on identity compromise, phishing, and misuse of legitimate access rather than advanced exploits. Industry studies also indicate that organizations using fragmented security tools take significantly longer to detect and contain incidents compared to those with integrated security operations.
For leadership teams, the questions that matter during an incident are practical and immediate:
- Can we detect identity compromise before it escalates into lateral movement or data exfiltration?
- Do we have unified visibility across endpoints, email, cloud applications, and user behavior?
- Are sensitive documents protected consistently, regardless of where they are stored or accessed?
- Can we investigate and respond within hours rather than days?
When answers to these questions are unclear, exposure is usually greater than expected.
Fragmented Security Is Not Security
One of the most common failure patterns in Philippine enterprises is fragmented security operations. Email security is handled in one console. Endpoint alerts live in another. Identity logs are reviewed separately. Cloud activity is monitored elsewhere, if at all.
During steady-state operations, this fragmentation is manageable. During an incident, it becomes a liability.
Attackers exploit this gap. Identity compromise happens in one system. Malicious activity unfolds in another. Detection occurs late because signals are never correlated. By the time teams piece the story together, business impact has already occurred.
Security teams are then forced into reactive coordination, manually stitching together logs and timelines while the business waits for answers.
In 2026, fragmented security tooling is not a neutral state. It actively increases risk.
Unified Security Operations as a Strategic Requirement
Modern environments require Unified SecOps, where identity, endpoint, email, cloud, and data signals are analyzed together, not in isolation.
This does not mean “one tool does everything” in a simplistic sense. It means:
- A single operational view of incidents across identity, devices, collaboration, and workloads
- Correlated detection that understands how one event leads to another
- Coordinated response that can contain threats without shutting down productivity
Microsoft and other industry research consistently show that organizations with unified detection and response reduce mean time to contain incidents dramatically compared to those relying on siloed tools.
The goal is not visibility for its own sake. It is decision confidence under pressure.
What Security Teams Need to Validate and Why It Matters
In hybrid and cloud-first environments, security readiness is revealed during incidents, not assessments. Most successful attacks exploit gaps that already exist across identity, visibility, and response coordination.
Security leaders must therefore validate whether controls actually work together under real-world conditions.
Identity as the Primary Attack Surface
In cloud-first environments, identity is the most frequently targeted entry point. Compromised credentials allow attackers to operate as legitimate users across SaaS and collaboration platforms.
Why this matters: Weak or inconsistently enforced identity controls enable lateral movement and data access without triggering traditional alerts.
What leaders should validate:
- Risk-based access enforcement, not static rules
- Strong governance of privileged identities
- Clear visibility into sign-in behavior and session risk
Endpoint and Workload Visibility
User devices and cloud workloads are common execution points once access is gained.
Why this matters: When endpoint and workload telemetry is fragmented, security teams cannot correlate identity events with execution behavior, delaying containment.
What leaders should validate:
- Consistent monitoring of endpoints and workloads
- Correlation between device activity and user identity
- Rapid isolation capabilities without widespread disruption
Data Protection and Insider Risk Exposure
Enterprise data is now accessed primarily through collaboration platforms rather than centralized repositories.
Why this matters: Data leakage often occurs through legitimate access paths, making it difficult to detect without contextual controls.
What leaders should validate:
- Consistent classification and protection of sensitive data
- Auditable access across collaboration platforms
- Behavioral indicators for elevated insider risk
Incident Response and Operational Readiness
Detection alone does not limit impact. Response speed and coordination determine business disruption and recovery cost.
Why this matters: Manual or poorly coordinated response increases dwell time, operational downtime, and reputational exposure.
What leaders should validate:
- Clearly defined response playbooks for identity-driven incidents
- Automation for common containment actions
- Alignment between IT, security, legal, and leadership during escalation
Security as a Continuous Control Layer
In modern environments, security cannot function as a final checkpoint. When controls are integrated across identity, endpoints, applications, and data, organizations gain earlier detection, faster response, and clearer accountability.
When security remains fragmented, every new capability increases risk.
Security readiness is no longer solely a technical concern. It is a leadership responsibility that directly affects resilience, regulatory confidence, and the organization’s ability to innovate without interruption.
From More Tools to Better Control
As security becomes inseparable from daily work, the challenge shifts from deploying more controls to deciding where focus and investment actually reduce risk.
These prioritization decisions, especially around identity, collaboration security, and unified SecOps, are examined further in Modern Work Security Priorities for Philippine Organizations in 2026, where we outline how enterprises reduce blast radius without slowing the business.
Could Your Business Withstand a Major Security Incident in 2026?
Industry research shows that organizations without integrated security operations take significantly longer to recover from ransomware and identity-driven attacks, often measured in weeks rather than days.
Where does your organization stand?
Identify gaps across identity, visibility, response, and recovery before an incident defines them for you.
Bringing the Four Together: What 2026 IT Readiness Really Requires
By 2026, IT readiness is no longer defined by isolated technology decisions. Migration, Modern Work, AI, and security now function as a single, interdependent system, where weakness in one area constrains progress in the others.
Migration establishes where workloads and data reside, but without architectural intent it introduces complexity rather than flexibility. Modern Work shapes how employees interact with information every day, but without governance it produces activity without measurable value. AI promises productivity and insight, but only when data, identity, and access foundations are sound. Security ultimately determines whether all of these capabilities can operate at scale without introducing unacceptable operational or compliance risk.
Organizations that progress with confidence toward 2026 are not those moving fastest, but those making deliberate trade-offs. They recognize that every decision expands one capability while constraining another, and that progress depends on sequencing change rather than pursuing initiatives in parallel.
Recognizing misalignment is only the first step. The harder challenge for IT leaders is deciding where productivity gains justify additional risk, which security controls are non-negotiable, and how to move forward without stalling the business. These decisions increasingly define the difference between environments that merely function and those that remain resilient as expectations rise.
And for that, you need the right partner!
Why Tech One Global Philippines
Executing this level of integrated planning requires more than technical expertise. It requires a partner that understands how global platforms operate within Philippine regulatory, operational, and risk contexts.
Tech One Global works with enterprises across the Philippines and South Asia to design, implement, and secure Microsoft-aligned environments that support real business outcomes. Our experience spans Cloud Migration, Modern Work Optimization, Enterprise Security, and AI-Readiness, delivered in environments shaped by local compliance requirements and evolving threat conditions.
As 4-time Microsoft Partner of the Year with 6/6 Microsoft Solutions Partner Designation in Modern Work, Security, Azure (Data & AI), Azure (Infrastructure), Azure (Digital & App Innovation), and Business Applications, we empower Philippine organizations to:
- Define Strategic Trajectories: Establish clear roadmaps for platform consolidation and cloud migration.
- Enforce Security Baselines: Implement robust, non-negotiable security standards across the enterprise.
- Optimize AI Preparedness: Develop a pragmatic framework for the safe and effective adoption of Microsoft Copilot.
- Mitigate Operational Risk: Sequence digital initiatives to ensure progress without compromising business continuity.
Our objective is not acceleration for its own sake, but the cultivation of a resilient foundation. We help organizations enter 2026 with an infrastructure that inherently supports long-term productivity, security, and stakeholder trust.
Request a Modern Work Readiness Assessment
Prepare for 2026 with confidence, supported by specialists who understand local threat patterns, compliance requirements, and operational constraints.
👉 Schedule yours today!